Most fraud stories have a clear victim. Someone checks their bank account and finds charges they never made. Someone gets a call about a debt they never took on. Someone discovers their name on accounts they never opened.
Synthetic identity fraud is different. In most cases, there is no victim who notices. No one calls to report it. No one monitors the account for suspicious activity.
That is exactly what makes it the fastest-growing financial fraud in the United States, and one of the hardest to stop.
What Is Synthetic Identity Fraud?
Synthetic identity fraud is the creation of a fictitious identity by combining real stolen data with fabricated information, then using that identity to open accounts, access credit, and commit financial crime.
Unlike traditional identity theft, where a criminal steals and impersonates a real person, synthetic fraud creates a person who has never existed. A real Social Security number belonging to a child or elderly person gets paired with a fake name, a fabricated date of birth, and an invented address. The result is an identity that looks legitimate across most verification systems because parts of it genuinely are legitimate.
This is why synthetic identity fraud is sometimes called Frankenstein fraud. The identity is stitched together from pieces of real and invented information until it appears whole.
Synthetic identity fraud is the fastest-growing type of financial crime in the United States. U.S. lenders faced over $3.3 billion in exposure to synthetic identities tied to new accounts in 2024, and estimated annual losses across the US economy range from $20 billion to $40 billion. Sophisticated fraud attempts nearly tripled to 28% of all fraud attempts in 2025, and 95% of synthetic identities go undetected during the onboarding process.
How Synthetic Identity Fraud Works
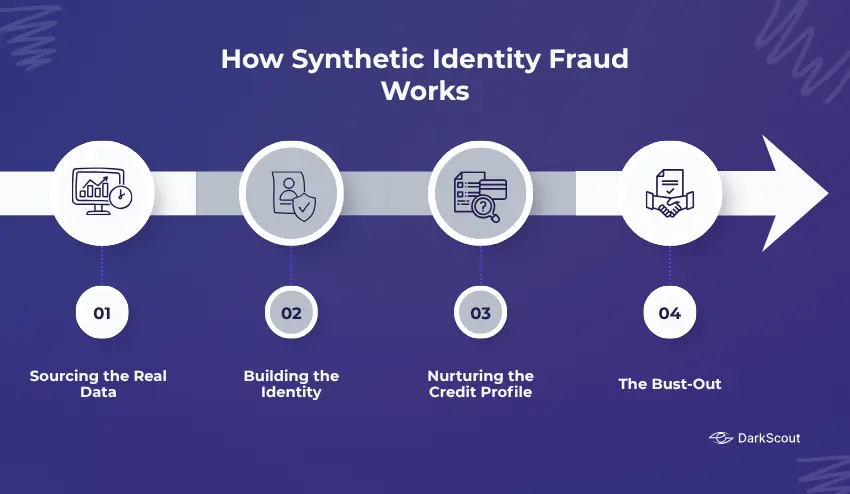
This is a slow, meticulous, and in some cases may even take up to several years for this final phase to fully conclude. The method goes something like this:
Stage 1: Sourcing the Real Data
Each synthetic identity requires at least one legitimate piece of information to start with. Social security numbers are ideal because they can be verified against the federal government and credit bureaus, legitimizing the synthetic identity from its creation.
Fraudsters source these SSNs in several ways. Data breaches that expose millions of records are one major pipeline. Dark web marketplaces where stolen credentials are sold in bulk are another. Children, elderly individuals, deceased people, and recent immigrants are disproportionately targeted because their SSNs have thin or dormant credit files. A child’s SSN has a clean history and will not be checked by its owner for years, sometimes decades.
The person who steals the SSN and the person who builds the synthetic identity are often not the same criminal. There is an entire underground economy around this. Specialists steal and sell SSNs. Separate specialists buy them and construct synthetic identities. The stolen data passes through criminal supply chains before it is ever used to commit fraud.
Stage 2: Building the Identity
Once a valid SSN is obtained, fraudsters attach fictional biographical details. A fake name. A fabricated date of birth. An invented address. Contact details that route back to the fraudster or to a burner account.
Some operations go further. They create social media profiles for the synthetic identity, build out professional histories on LinkedIn, and establish a digital footprint designed to make the fake person appear real across multiple platforms. This is known as backstopping, and it is becoming increasingly common as verification methods improve.
The first credit application will typically be rejected because the applicant has no credit history. But that rejection itself creates a file at the credit bureaus. The fraudster now has something to build on.
Stage 3: Nurturing the Credit Profile
This is the long game. The fraudster applies for a secured credit card, becomes an authorised user on existing accounts, or opens Buy-Now-Pay-Later accounts. Every bill gets paid on time. Every account stays in good standing.
Over six to eighteen months, the synthetic identity builds a credit history that looks entirely legitimate. Credit limits increase. New accounts get approved. The fake person becomes, on paper, a model borrower.
During this phase, there is nothing to detect because nothing appears wrong. The payments are real. The account activity is normal. Traditional fraud detection has no mechanism to identify this because no victim is complaining, and no rules are being broken yet.
Stage 4: The Bust-Out
This is the moment all of that patient credit-building was working toward.
In a coordinated burst, the fraudster maxes out every line of credit simultaneously. Withdraws maximum cash advances. Takes out the largest possible loans. Then disappears entirely.
There is no person to chase. The name is fake. The address was a mailbox. The phone number was a burner. The identity that owed all this money never existed. Lenders write off the losses as bad debt, and the fraud often goes undetected for so long that even the investigation leads nowhere.
The average loss per confirmed synthetic fraud case is $15,000. Organised rings run dozens or hundreds of synthetic identities simultaneously, scaling those losses dramatically.
Who Gets Hurt by Synthetic Identity Fraud?

The most counterintuitive aspect of synthetic identity fraud is that it appears to have no direct victim. But the harm is real and widespread.
- Children – A child’s SSN used to build a synthetic identity can result in that child reaching adulthood to discover a damaged credit history, debts in their name, and a legal nightmare to untangle before they ever apply for their first loan or apartment.
- Financial institutions – The financial institutions – the banks, lenders, and fintechs – incur the direct costs of synthetic borrowers who default. In most cases, these losses are taken as bad debt, since the synthetic identity cannot be detected until it is far too late.
- Consumers – In order to cover losses to fraud of this kind, financial institutions raise interest rates for all customers, establish stricter criteria when making loans, and introduce more procedures that cause customers aggravation when opening accounts.
- Government benefits – Synthetic identities are being used on an increasing scale to claim unemployment benefits, tax rebates, healthcare services, and pandemic aid. It is estimated that 0.08% of government benefit payments are the result of fraudulent, synthetic identities, and this costs public funds $283 million a year.
- Health systems – Doctors’ offices, clinics, and other health care organizations are providing services, medications, and medical equipment to synthetic identities and then selling the items.
Synthetic Identity Fraud vs Traditional Identity Theft
These two kinds of fraud are almost always mixed up; they are two distinctly different kinds of crime.
These two kinds of fraud are almost always mixed up; they are two distinctly different kinds of crime. The criminal uses your actual name, your real Social Security number, your genuine address, and accesses your existing accounts or opens new ones in your name. You, as the victim, are likely to notice. Unexpected charges appear. Credit applications you never made show up in your file. A debt collector calls about something you have no knowledge of.
Synthetic identity fraud creates a person who does not exist. There is no victim to notice because no real person’s existing financial life is being disrupted. The fraud runs silently until the bust-out, at which point the fraudster vanishes and the lender discovers the identity was never real.
This distinction is precisely why synthetic fraud is so much harder to detect and prosecute. Victim complaints are one of the most effective fraud detection mechanisms available to financial institutions. Synthetic identity fraud removes that mechanism entirely.
| Traditional Identity Theft | Synthetic Identity Fraud | |
|---|---|---|
| Victim | Real person whose identity is stolen | No direct victim |
| Identity used | Existing, complete real identity | Fabricated, never existed |
| Detection trigger | Victim reports suspicious activity | No natural detection trigger |
| Time to discover | Often quick, victim notices | Months or years |
| Recovery | Possible through fraud claims | Losses often unrecoverable |
The Dark Web Connection
Synthetic identity fraud does not happen in isolation. It depends entirely on a supply of stolen real data, and that supply flows through dark web markets.
After major data breaches, millions of Social Security numbers, dates of birth, and addresses get bundled into datasets and sold on criminal marketplaces. Fraudsters browse these markets looking for clean SSNs, particularly those belonging to children or people with thin credit files. They can purchase specific profiles to order depending on what kind of synthetic identity they want to build.
The process has become industrialised. Crime-as-a-Service networks now sell identity assembly toolkits that automate the construction of synthetic identities at scale. A single operator can build and manage dozens of synthetic identities simultaneously using tools purchased from these underground services.
This dark web pipeline is why monitoring for your personal information on criminal marketplaces matters, not just for you personally but for your children. A child’s SSN appearing in a dark web data dump is an early warning that it could be used to build a synthetic identity long before that child is old enough to apply for credit themselves.
How AI Is Making Synthetic Identity Fraud Worse
The threat was already large enough; AI has made it vastly larger.
AI can create photorealistic fake identification documents, Utility bills, and fake selfies that beat liveness tests in digital onboarding. Deepfakes have increased by 500% since 2024, and deepfake fraud cost 25.1 billion dollars in losses in 2025. The proportion of worldwide recorded frauds due to fakes created with AI were 2% of all documented frauds globally in 2025 and negligible a year earlier.
AI allows the scale of synthetic identities. An activity that once would have taken human effort can be automated, generating dozens of identities with their own support documents to apply to dozens of institutions at once with these new tools.
64% of financial institutions say that AI and deepfakes are their greatest concerns regarding fraud in 2025. Fraud prevention strategies built around human-scale fraud efforts have no capacity to deal with the volume of fraud that machine-scale attacks produce.
Industries Most Vulnerable to Synthetic Identity Fraud
The impact of synthetic identity fraud can span any industry where an account is opened, credit extended, or service provided based on identification.
- Financial services are arguably most at risk. Lenders, fintech firms, and banks fall directly into this category. 67% of financial institutions surveyed have reported increases in fraud levels in 2025, and 40% say they see synthetic identity fraud as one of their top risks. Synthetic identities represent 80% of all new account fraud in financial institutions.
- Healthcare has increasingly become a target, with fraudsters using synthetic identities to gain medical care, high-value prescription drugs, and medical devices that can then be sold on the black market.
- Government programmes such as social security benefits, tax refunds, unemployment benefits, and pandemic relief funds are all being targeted with synthetic identities.
- Telecommunications is another growing sector, with criminals using synthetic identities to open accounts, apply for device financing, or to secure telephone services.
- E-commerce and retail are at risk from synthetic identity fraud occurring during returns processes, in loyalty programs, and with credit account abuse.
How to Protect Yourself and Your Family
Most people do not know that their data is at risk until damage has already been done. Proactive monitoring is the most effective individual defence.
- Monitor your credit reports regularly. Check all three bureaus for accounts, inquiries, or activity you do not recognise. Unexpected credit applications or unfamiliar account openings are early warning signs.
- Check your children’s credit. Children should have no credit file. If a credit report exists for your child, it is a serious red flag that their SSN may have been compromised and used in a synthetic identity scheme.
- Place a credit freeze on your children’s Social Security numbers. All three major bureaus allow parents to freeze credit files for minors. A frozen file cannot be used to open new accounts, which stops synthetic identity building before it starts.
- Monitor the dark web for your data. Your SSN and personal information may already be circulating in criminal markets without your knowledge. Dark web monitoring services watch for your credentials continuously, alerting you the moment your information surfaces in breach data or dark web sales listings.
- Be cautious about where you share personal information. Phishing emails, fake websites, and data collection by untrustworthy services are all vectors through which personal data gets stolen and eventually ends up in the hands of synthetic identity fraudsters.
What Businesses Can Do
If your organisation offers credit or opens accounts, you’ll likely face synthetic identity fraud. Many fake identities slip through, as the data provided on applications seems genuine, but it belongs to no one.
Your organization should use a multi-layered approach to combat this. Comparing data points from a variety of sources helps reveal data inconsistencies that would go unnoticed during single checks.
Behavioral analytics will help identify anomalous activity, such as credit being built very rapidly. Identifying commonly shared personal details, such as cell phone numbers or devices, will also reveal fraud rings.
Collaboration between institutions with data sharing provides an additional level of security. One institution can identify a synthetic identity, and the others can prevent any damage.
For further security measures, services such as DarkScout can help you be alerted to threats on the dark web and outside of your organization.
The Bottom Line
Synthetic identity fraud works because it is designed to be invisible. There is no victim to report it. No alert fires. No rule gets broken until the very end, when the fraudster has already vanished.
The stolen Social Security numbers that fuel this fraud do not appear from nowhere. They come from data breaches, dark web sales, and credential theft operations that have been feeding criminal markets for years. Every breach that exposes personal data creates raw material for synthetic identities that may not be used for fraud until years later.
Early warning matters. Knowing that your data or your children’s data has appeared in criminal markets gives you a window to act before a fraudster builds a years-long credit history on it.