Every business, no matter its size, is sitting on data that cybercriminals want. Customer records, financial files, employee credentials, internal communication, all of it has value on the darknet. And most companies have no clear idea how exposed they actually are.
That’s where a cybersecurity risk assessment comes in.
It’s not just a compliance checkbox or a document that collects dust after an audit. A proper cyber risk assessment tells you exactly where your weaknesses are, what threats are most likely to exploit them, and what you should do about it, before something goes wrong.
This guide walks you through everything: what a cybersecurity risk assessment actually is, why it matters more than ever in 2026, and how to conduct one for your business step by step.
What Is a Cybersecurity Risk Assessment?
A cybersecurity risk assessment is an ordered process for understanding, analyzing, and responding to threats to the digital assets, data, and systems within an organization.
Imagine a complete security audit of your organization, but rather than following a checklist, you build a complete and detailed picture of what could happen, how probable it is to happen, and the actual effect it would have.
A complete and total eradication of all risks is an unattainable goal; the aim is to have sufficient knowledge of risks present to enable informed and calculated decision-making regarding resource allocation, threat prioritization, and other aspects of security posture management.
A cybersecurity risk assessment typically covers:
- Digital assets: the data or systems that require protection
- Threat identification: what could attack or compromise those assets
- Vulnerability assessment: the gaps within those defenses
- Risk analysis: the probability and probable impact associated with each identified risk
- Mitigation planning: the necessary controls or procedures that should be implemented
It is important to understand the difference between risk and vulnerability: a vulnerability is a weakness (an unpatched server, weak passwords, incorrectly configured cloud buckets) that can be used to compromise the integrity of a system; risk represents the probability of that weakness being exploited, and the potential impact associated with it. A solid cyber risk assessment must tie these two concepts together.
Why Does Your Business Need One?
The reality is, most businesses don’t recognize that a significant security problem exists until a breach has already happened. By then, the damage has been done.
The numbers themselves bear this out in no uncertain terms. According to IBM’s 2024 Cost of a Data Breach Report, the average cost of a data breach globally was $4.88 million – a record high. Even a fraction of that amount could be catastrophic for a small business. Research conducted by Forbes has found that 60 percent of small businesses fold within six months of suffering a cyberattack.
A cybersecurity risk assessment helps you get ahead of that reality instead of reacting to it.
Beyond financial protection, there are several other reasons businesses run regular assessments:
- Regulatory Compliance: Many industry-specific compliance requirements, like GDPR, HIPAA, ISO 27001, and SOC 2, mandating documented risk assessments are enforced. Failure to conduct such assessments would not only be a security loophole but a legal one as well, with subsequent legal and financial penalties.
- Better Security Spending: It would be foolhardy to spend resources without identifying where actual threats exist. Risk assessments enable your business to deploy resources in areas that need them most.
- Brand Protection: Your reputation is everything, and it’s easily destroyed by a single breach that compromises client data. Risk assessment is key to preserving your brand.
- Business Resilience: Awareness of your specific risks allows you to formulate and implement strategies for dealing with eventualities such as quicker recovery, lesser downtime, and business continuation under adverse conditions.
For any organization that stores any kind of sensitive information, such as customer records, payment details, employee data, intellectual property, or trade secrets, a cybersecurity risk assessment is non-negotiable.
Common Cyber Threats You Need to Assess
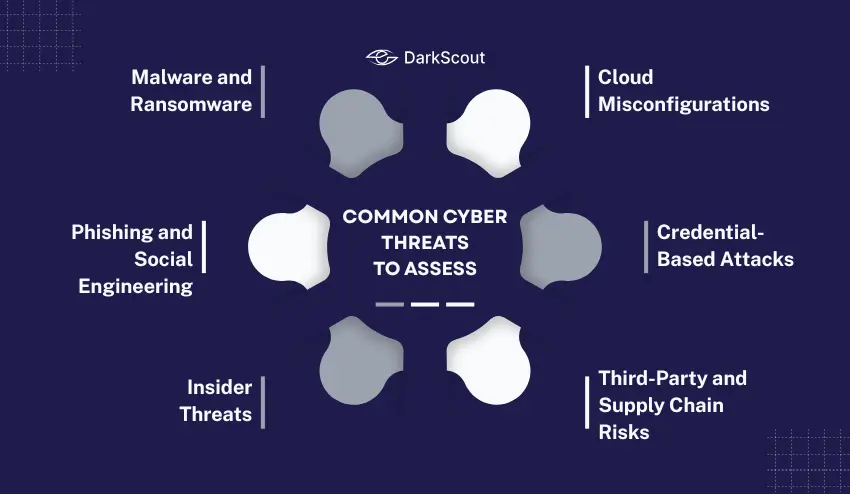
Before you can assess your risk, you need to understand what you’re assessing against. These are the threats that show up most consistently in risk assessments across industries.
- Malware and Ransomware: These malicious software programs can compromise or completely shut down your systems. Ransomware is one of these types of software, as it will encrypt and lock your data and then request money to release this data. The threat has rapidly increased again in 2025, with data exfiltration occurring in almost 96% of encrypted attacks. Finding out what threat hunting is can benefit your team in spotting threats early.
- Phishing and Social Engineering: The most frequently encountered cyber attack is phishing. With these kinds of emails, criminals try to convince employees to give up their passwords and click on malicious links that may even look like one from your executive or a trustworthy vendor. Email spoofing is also closely related to this threat, as it may also give the criminal some aid.
- Insider Threats: A threat does not always come from an external party. Your systems and data can be at risk from frustrated former employees, untrusted contractors, or compromised internal user accounts. The danger of Insider Threats are they possess legitimate access to systems and data and require little more than a user name and password to proceed with their malicious intents.
- Cloud Misconfigurations: One of the most significant causes of data exposure has become the misuse of cloud infrastructure with inadequately configured storage buckets, permissions, and cloud services. Misconfiguration of the cloud has become one of the most frequent and avoidable cybersecurity failures currently happening.
- Credential-Based Attacks: Stolen or leaked login credentials are bought and sold on darknet marketplaces every day. Attackers use them for account takeovers, credential stuffing, and lateral movement through your network. This is why understanding what happens to your data on the dark web matters, which we’ll cover later in this guide.
- Third-Party and Supply Chain Risks: Your business will be only as strong as your weakest link within the vendor ecosystem, and while your own system could be perfectly secure, the risk of being a victim of an attack still lies if one of your suppliers or software suppliers systems is compromised.
How to Conduct a Cyber Risk Assessment: Step by Step
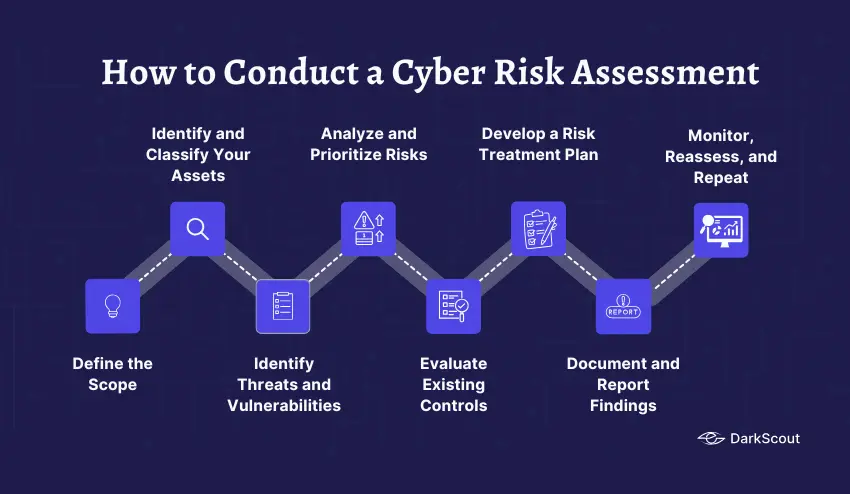
There’s no universal template that works for every organization, but effective cybersecurity risk assessments follow a consistent process. Here’s how to do it properly.
Step 1: Define the Scope
Before you begin the process of risk cataloging, you must determine what you are cataloging. This includes defining the boundaries around the scope of this assessment – which systems, which departments, which physical locations, which types of data are involved?
When dealing with very large organizations, taking a comprehensive assessment all at once will likely become unwieldy. It is much more practical to focus initial risk cataloging on the most important systems first, or on the systems that store the most sensitive data, and then expand on that later.
Key questions to answer at this stage:
- What business processes are in scope?
- Which networks and systems are included?
- What types of data do we need to protect?
- Is third-party involvement part of the assessment?
Step 2: Identify and Classify Your Assets
You cannot protect what you do not know you have. The second step of risk cataloging is to make a list of all the relevant assets your business has. This includes things such as the hardware you own, software that you use, your data (customer lists, financials, etc), networking devices you own, and the cloud services that you utilize.
After you have listed all your assets, you must then classify each asset according to its critical importance. Not all assets are equally valuable. Your customer database is much more important than your company calendar. Your payment processing system has more inherent risk associated with it than your break room wifi. You have to prioritize where your security assets and money should be focused.
Step 3: Identify Threats and Vulnerabilities
At this core stage, two interconnected questions are asked: What kinds of things can attack or harm our assets? And what are the weak points within our systems that would allow such an attack to occur?
Threats come from many sources, including historical data of your organization’s incidents, threat intelligence reports, regulatory requirements, and the knowledge of your security team. Typical threats that will be identified are the same as listed previously: malware, phishing, insiders, supply chain threats, and so on.
A vulnerability assessment dives deep into your actual systems to identify weaknesses before the bad guys can. The primary methods for identifying vulnerabilities are a combination of automated vulnerability scanning tools, penetration testing, and manual security reviews. Look for missing patches, poorly configured services, insufficient user permissions, weak authentication practices, and a lack of network segmentation, etc.
Step 4: Analyze and Prioritize Risks
Now that we have our threats, vulnerabilities, and assets identified, we can start to connect them. For each identified pair of threats and vulnerabilities, two scores are assigned: likeliness (probability of the threat being exploited against the vulnerability) and impact (severity of the incident should it occur).
A simple risk matrix works well here:
| Likelihood \ Impact | Low | Medium | High |
|---|---|---|---|
| High | Medium Risk | High Risk | Critical |
| Medium | Low Risk | Medium Risk | High Risk |
| Low | Minimal | Low Risk | Medium Risk |
This framework separates the critical risks that should be addressed immediately from those that can wait for remediation at a later stage. Not all vulnerabilities need to be fixed with the same urgency and budget; risk prioritization ensures your security resources are directed appropriately.
When assessing the risk, it is useful to consider beyond merely the technical implications of an incident; don’t forget the business, regulatory, reputational, and financial impact of the breach.
Step 5: Evaluate Existing Controls
Before attempting treatment of the threats and vulnerabilities, look at what security controls you already have in place and assess whether they’re good enough to mitigate against those threats and vulnerabilities. Existing controls normally cover aspects such as firewalls, endpoint security, access controls, data encryption, backup and recovery, training, and so on.
You need to identify gaps where controls simply don’t exist or areas where existing controls are not effective or properly maintained. These two things are equally important.
Step 6: Develop a Risk Treatment Plan
Once you know what your risks are and how well your current controls address them, you have four options for each risk:
- Mitigate: Implement controls to reduce the likelihood or impact of the risk
- Accept: Acknowledge the risk exists and decide it’s within your tolerance level
- Transfer: Shift the financial burden, typically through cyber insurance
- Avoid: Change business practices to eliminate the risk entirely (for example, stop collecting certain types of sensitive data you don’t actually need)
Most risks get mitigated. Your treatment plan should document exactly what controls will be implemented, who is responsible for implementing them, and by when. Without ownership and deadlines, mitigation plans tend to stall.
Step 7: Document and Report Findings
A good risk assessment should yield a clear and actionable report, not a multi-hundred-page technical document that no one reads. Tailor the presentation of findings to two primary audiences: your technical security team and the senior leadership of the organization. The former needs the technical details and remediation recommendations, whereas the latter requires a strategic view of the organization’s risk profile and a justification of security resource allocation.
Your report should contain an executive summary highlighting the top critical risks, the full risk register (listing all identified risks and their scores), the evaluation of current controls, and the proposed remediation plan with assigned ownership and target dates. Depending on any framework or standards you adhere to, you may also want to include compliance mapping.
Step 8: Monitor, Reassess, and Repeat
A cybersecurity risk assessment is not a static document; it must be a dynamic process. The security landscape is constantly changing, systems are updated, vendors change, and new vulnerabilities are disclosed daily.
As such, your organization should aim to implement regular monitoring of its risk position to detect significant changes and plan annual (at minimum) reassessments, potentially more frequently if the organization experiences a significant business change (e.g., a merger, new system deployment, a security incident).
Cybersecurity Frameworks That Guide Risk Assessments
You don’t have to build your risk assessment methodology from scratch. Several well-established frameworks provide structure and credibility to the process.
The NIST Cybersecurity Framework (CSF) is probably the most common framework in the industry worldwide. The framework outlines a four-stage approach to performing risk assessments, involving preparatory stages of the assessment, the assessment itself, communicating findings, and continuous monitoring.
ISO 27001 / ISO 27005 – The ISO international standards provide for Information Security Management practices and, in particular, ISO 27005deals specifically with Information security risk management, providing a guide especially relevant for organizations pursuing ISO 27001 certification.
NIST SP 800-30 – A comprehensive guide to conducting risk assessments for federal information systems, though extensively referenced for the private sector as a robust guide.
SOC 2 – If your organization delivers cloud or SaaS, being SOC 2 compliant necessitates having strong risk management in place, and regular risk assessments become a required control.
Using a recognized framework isn’t just about methodology. It also helps you demonstrate to customers, partners, and regulators that your risk management practices meet established standards.
How Often Should You Run a Cyber Risk Assessment?
The short answer: at least once a year, and more often if anything significant changes.
Most cybersecurity frameworks recommend annual risk assessment, but even waiting a year can leave you exposed, given the week-over-week changes in the threat landscape.
Beyond your annual assessment, you should also reassess when:
- New systems or cloud infrastructure are rolled out
- New vendors are brought on to handle sensitive data
- There are Mergers and Acquisitions, or other structural changes within the company
- Security incidents (breaches or close calls) occur
- Significant new vulnerabilities that are exploitable and relevant to your stack are disclosed
- Major changes in regulation or compliance that relate to your industry occur
Continuous monitoring fills the gaps that formal assessment can’t cover. Setting up automated monitoring of your assets, credentials, and exposure on the dark web will keep you from operating blind between risk reviews.
The Role of the Dark Web in Your Risk Assessment
Most cybersecurity risk assessments focus on what’s happening inside your network. But some of your biggest risks are already outside it, on darknet marketplaces and forums where your data may already be circulating.
When attackers breach a company, the stolen data doesn’t disappear. Within hours, it often ends up on dark web marketplaces: employee credentials, customer records, internal documents, and financial information. Criminals buy and sell this data, use it to launch follow-on attacks, or weaponize it for spear-phishing campaigns targeting your team.
Understanding your dark web exposure is now a critical component of a complete cybersecurity risk assessment. This means checking whether your organization’s credentials, email addresses, or proprietary information have already been compromised and are actively circulating in underground markets.
DarkScout’s Darknet Threat Assessment and Dark Monitoring services are built exactly for this. By continuously scanning darknet forums, marketplaces, and breach databases, DarkScout gives organizations real-time visibility into their dark web exposure, so that compromised data becomes an input to your risk assessment rather than a surprise that triggers an incident response.
You can also use DarkScout’s free email scan to quickly check whether your organization’s email addresses have already been exposed in known breaches. It’s a good starting point before a full assessment.
Understanding what darknet marketplaces actually are and how they operate helps you understand why this matters for your risk posture.
Cyber Risk Assessment Checklist
Use this checklist to make sure your assessment covers all the critical areas:
Scoping and Preparation
- Outline scope – systems, departments, data types, third parties, etc.
- Know who the important users are in IT, legal, compliance, and business.
- Select an assessment model (NIST CSF, ISO 27005, etc.)
- Establish risk tolerance levels with leadership
Asset Identification
- List all hardware, software, cloud and network elements.
- Note down any sensitive data that is used and stored.
- Identify third-party relationships and access to internal systems.
- Identify assets as critical to business operations
Threat and Vulnerability Identification
- Examine security incidents and near-misses from the past
- Review the latest threat intelligence sources and industry reports.
- Perform automated vulnerability scans on in-scope systems.
- Perform penetration testing of critical systems.
- Look for credentials or sensitive information on the dark web.
Risk Analysis
- Evaluate the potential for the risk to occur and the potential impact of the risk.
- Apply the risk matrix to score and prioritize risks
- Review current controls and determine control deficiencies
- Determine inherent and residual risk for critical items
Mitigation and Reporting
- Create a risk treatment plan that includes mitigation actions, owners and deadlines.
- Document compliance mapping to relevant regulatory frameworks
- Create an executive summary to present to leadership.
- Develop a comprehensive technical team risk register
- Set up a monitoring and re-evaluation plan.
Conclusion
A cybersecurity risk assessment isn’t something you do once and forget about. It’s an ongoing practice that gives your organization clarity: clarity about what you’re protecting, what threatens it, and what you’re actually going to do about it.
The businesses that handle cyber threats well aren’t the ones with the biggest budgets. They’re the ones with the best visibility. They know their assets, understand their risks, and have a plan that gets updated as the threat landscape changes.
Start with what you have. Define your scope, map your assets, identify your biggest threats, and prioritize. Even an imperfect first assessment is infinitely better than no assessment at all, and it gives you a baseline to build from.
And remember: the risk picture doesn’t stop at your network perimeter. What’s happening on the dark web with your organization’s data is part of your risk posture too. Make sure your assessment accounts for it.