Building a serious in-house security program is expensive. A fully staffed Security Operations Center running 24/7 costs millions annually. Senior security analysts are in short supply globally. And the threat landscape doesn’t pause while you hire, onboard, and train.
For most organizations, that gap between the security they need and the security they can realistically build has become a real business risk.
Cybersecurity as a Service (CSaaS) exists to close that gap. It gives businesses access to enterprise-grade security capabilities, delivered by specialists, through a subscription model that scales with the organization rather than requiring years of internal program-building to get there.
This guide covers everything you need to know: what CSaaS actually is, what’s included, how it compares to in-house security, who it’s right for, and how to choose a provider that will actually protect you rather than just sell you a subscription.
What Is Cybersecurity as a Service?
Cybersecurity as a Service, also known as CSaaS, is an outsourced IT security model that offers access to security solutions hosted by a third party through the cloud. Rather than build its own security capabilities internally (staffing and investing in tools and technologies), the company will subscribe to a managed service to perform monitoring, threat identification, incident response, compliance assistance, and so on.
In essence, CSaaS is to owning your power plant as paying an electricity bill is to owning your power plant. The desired outcome is the same-power is available-but the investment, the complexity, and the labor involved are significantly different.
Operationally, a CSaaS vendor would run its security operations center (SOC) to monitor, detect threats, and manage responses on your behalf using a mix of security tools, automation, threat intelligence, and human analysts. By doing so, the client can gain security protection without the cost of building a full security team, the investment required to maintain a collection of security tools, or developing the underlying processes to bring it all together.
A CSaaS is not an individual product, but rather a service model that encompasses a package of security capabilities such as endpoint security, network security monitoring, threat detection and response, vulnerability management, identity security, compliance, and in the case of some providers, dark web monitoring. Which services are included depends on the service provider and your chosen package or tier.
The most fundamental aspect of CSaaS is bridging the gap between threats of an enterprise-level size and organizations that are typically lacking enterprise-level security resources.
CSaaS vs SECaaS: Is There a Difference?
You’ll see both terms used, sometimes interchangeably, and the distinction is worth clarifying.
CSaaS (Cybersecurity as a Service) is the broader umbrella term. It refers to the full outsourced cybersecurity model: the combination of technology, people, and processes delivered as a managed service.
SECaaS (Security as a Service) is often used more narrowly to describe individual security capabilities delivered via the cloud as standalone services, such as a cloud-based firewall, identity management, or email security platform, without necessarily including the full managed service wrapper of human analysts and integrated operations.
In everyday usage, most vendors and analysts treat the terms as equivalent. The more important question isn’t what you call the model but what’s actually included: are you getting technology only, or are you getting technology plus the human expertise to operate it effectively?
The most effective CSaaS engagements combine both: cloud-delivered security tools supported by experienced analysts who monitor, investigate, and respond, not just alert.
Why the Demand for CSaaS Is Exploding
The cybersecurity skills gap is getting worse.
- It is estimated that there are 3.5 million unfilled cybersecurity jobs worldwide.
- The number of positions available in the cybersecurity field in the US is much larger than the number of qualified professionals.
- Companies that can attract talent in the form of skilled analysts frequently find themselves in a situation where they can’t keep that talent around because of:
- High salary competition
- Competitive recruiting efforts.Intense recruiting from rivals.
- Burnout and turnover
- It is more and more costly and challenging to maintain an internal security team.
The price of cyberattacks continues to grow.
- Cyber attacks are increasingly causing significant financial damage annually.
- As per the IBM Cost of a Data Breach Report:
- The cost of an average breach worldwide hit an all-time high of $4.88 million.
- A significant breach can be a death knell for many SMBs.
- Proactive security investment is today seen as much more cost-effective than having to deal with breach recovery.
The attack surface has grown a lot in the modern era.
Today’s organizations need much more than just office networks.
Key drivers include:
- In remote and hybrid work environments.In remote and hybrid work settings.
- Cloud migration
- Increased SaaS adoption
- IoT device expansion
- Integrations and vendor ecosystems by third parties
This creates:
- You can set up more endpoints to monitor. Set up more endpoints to monitor.
- A greater number of identities to be secured.
- More potential vulnerabilities
- Greater operational complexity
Many internal security teams can’t scale as quickly as they need to handle this exposure.
Organizations Are Increasingly Turning to Outsourced Security
- According to industry research, 82% of organizations are looking to speed up security outsourcing.
- Security is not a non-issue for businesses that are outsourcing.
- Better coverage
- Faster response times
- 24/7 monitoring
- Having access to experienced experts.
- Lower operational costs
With CSaaS, organizations can gain access to enterprise-level security features without the need of a large in-house team.
The Market Growth Reflects a Long-Term Industry Shift
- In 2026, the managed security services market was estimated to be worth around $45 billion.
- It is expected to reach more than $80 billion by 2030.
- This is a sign of the wider trend in organizations’ approach to cybersecurity:
- From ownership-based security models
- A scalable, service-based approach to security operations.
For many companies, CSaaS is not just a viable support; it’s the most practical approach to managing effective cybersecurity at scale.
Core Components of Cybersecurity as a Service
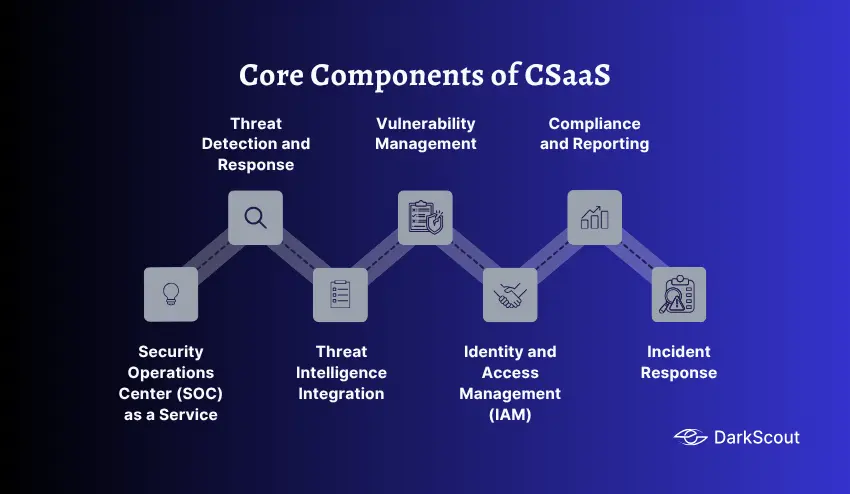
1. Security Operations Center (SOC) as a Service
The SOC is the operational heart of any CSaaS program. A managed SOC provides 24/7 monitoring, alert triage, investigation, and incident response by teams of experienced analysts. For organizations that couldn’t justify building their own SOC, this is arguably the single most transformative thing CSaaS delivers: round-the-clock human expertise watching their environment constantly.
2. Threat Detection and Response
CSaaS providers deploy and manage the technology stack that identifies threats: Security Information and Event Management (SIEM) systems that aggregate and correlate logs across your environment, Endpoint Detection and Response (EDR) tools that monitor device-level behavior, and Extended Detection and Response (XDR) platforms that connect signals across endpoints, networks, email, and cloud into a unified threat picture.
3. Threat Intelligence Integration
Good threat detection requires context. CSaaS providers continuously integrate external threat intelligence: indicators of compromise, known malicious IP addresses, emerging attack techniques, and intelligence from dark web monitoring into their detection systems. This context is what separates a provider that can detect novel attacks from one that only catches threats they’ve seen before.
4. Vulnerability Management
A continuous scanning process across the organization, designed to find unpatched software, incorrectly configured services, and vulnerabilities, before attackers have the opportunity to weaponize them. A good CSaaS solution should provide more than just an inventory of the vulnerabilities in your network; it should tell you which ones are actually being exploited on an ongoing basis by hackers against organizations such as yours and help you decide where to focus efforts in remediation.
5. Identity and Access Management (IAM)
Identity and Access Management involves controlling what access to what resources, with which individuals or systems, to assure a defined access policy and proper security controls are applied, is a fundamental security function. CSaaS offerings will often include, or allow integration of, IAM functions. This will typically include enforcing multi-factor authentication, ensuring privileged access and looking for aberrant behavior of users within the system.
6. Compliance and Reporting
Whether your organization is bound by regulatory compliance (e.g., HIPAA, SOX, PCI-DSS) or must follow a security framework (e.g., ISO 27001, SOC 2, GDPR), tracking and reporting the status of your compliance controls can be a significant operational hurdle. CSaaS offerings often include a reporting function for all of the individual control points so that compliance documentation for internal and external auditors can be generated without the need for manual collection.
7. Incident Response
When something goes wrong, speed matters. CSaaS providers include incident response capabilities, with defined processes for containment, eradication, and recovery that can be activated immediately without the delays that come from assembling an internal response team during a live incident.
Types of Cybersecurity as a Service
No single CSaaS solution fits every need. Companies can buy services that meet various aspects of their requirements, and many combine different types of services as well, depending on the existing capacity they have internally and their specific requirements.
1. Managed Detection and Response (MDR)
This type of CSaaS solution includes ongoing security monitoring, threat hunting, threat detection, and incident response, all within a single managed security service. MDR vendors offer this service with full use of their own Security Operations Center, staffed by security professionals and analysts who will continuously hunt and investigate active threats in your environment and respond on your behalf when a compromise occurs. MDR service is generally the best starting point for any company that lacks any kind of internal security operations capacity whatsoever.
2. Managed Security Services (MSS)
MSS is the broader category from which MDR evolved. MSS providers typically manage specific security tools and technologies on your behalf: firewalls, intrusion detection systems, SIEM platforms, and similar infrastructure. MSS tends to be more technology-focused and less analyst-intensive than MDR, making it better suited for organizations that already have some internal security capability and want to augment it with managed technology services.
3. SOC as a Service
The service level that fully covers your Security Operations Center needs. The SOC as a Service provider will be entirely responsible for the infrastructure, tools, and staffing needed for the SOC to run 24/7, without the client needing to invest in or develop any part of that functionality internally. Organizations looking for a SOC as a Service solution will likely have exceeded their current capabilities through MDR services, but may still feel that building their own SOC is out of reach, given the tens of millions required for infrastructure, tools, and staffing.
4. Vulnerability Management as a Service
Continuous scanning, assessment, and prioritized remediation guidance for vulnerabilities across your environment. Some providers include penetration testing (PTaaS, or Penetration Testing as a Service) as part of this offering, providing both automated and human-led testing of your defenses.
5. Identity as a Service (IDaaS)
Cloud-delivered identity and access management, covering single sign-on, multi-factor authentication, privileged access management, and user lifecycle management. IDaaS has become especially important as the perimeter has dissolved and identity has become the primary security boundary in cloud-first environments.
6. Dark Web Monitoring as a Service
A critical and often overlooked CSaaS category. Dark web monitoring services continuously scan darknet forums, marketplaces, ransomware leak sites, credential markets, and encrypted channels for your organization’s data, credentials, and sensitive information. This service addresses the threat landscape that exists outside your network, which traditional security tools can’t see at all.
7. Cloud Security as a Service
As organizations move infrastructure to the cloud, specialized cloud security services protect cloud environments, detect misconfigurations (one of the leading causes of data breaches), and enforce security policies across multi-cloud architectures.
How CSaaS Works

Learning what CSaaS looks like on a day-to-day basis will clear up what you’re actually purchasing and what the service actually offers.
Step 1: Onboarding and Assessment
All CSaaS engagements start with you telling us about your environment. The provider’s initial assessment of your current security posture, the identification and mapping of your infrastructure assets, what’s important to you, and your compliance needs, enables us to set up monitoring and detection on the customer’s specific environment rather than relying on universal, best-practices settings.
Step 2: Technology Integration
The provider integrates its security toolkit with your environment. Normally, this involves installing lightweight agents onto each endpoint, having server and network devices forward their logs to your provider’s SIEM, connecting to cloud provider APIs to get visibility of your cloud environment, and, if necessary, integration with any security tools you already possess. Today’s standard CSaaS offering typically complements, rather than replaces, existing tools.
Step 3: Continuous Monitoring
After integration is complete, your provider continuously monitors the entirety of your environment. Logs, events, traffic flowing through your network, unusual behavior from endpoint devices, and global threat feeds all flow into your provider’s detection system, which both automated processes and human analysts scan for indicators of compromise, potential malicious behavior, and live threats.
Step 4: Alert Triage and Investigation
When the system generates an alert, analysts investigate to determine whether it represents a genuine threat or a false positive. This triage function is one of the most valuable things a CSaaS provider delivers: experienced analysts who have investigated thousands of incidents can make that determination far faster and more accurately than an in-house team building that expertise from scratch.
Step 5: Response and Containment
Confirmed threats will trigger action from the provider. Actions taken may be notification and advice (for a less involved service) to a complete incident response where the provider will take actions to isolate affected endpoints, block malicious IPs, and disable any affected credentials or initiate an incident response plan.
Step 6: Reporting and Continuous Improvement
Regular reporting is provided by the CSaaS provider: Weekly or monthly reports about the threats, incidents for the impactful security events, and trends analysis over time to give you insight into your security posture. Reporting is used for operations to keep your staff informed, as well as governance to satisfy leadership and auditors of the security program’s effectiveness.
CSaaS vs In-House Security: An Honest Comparison
This is a question most security leaders ask at some point, and the honest answer isn’t always “go CSaaS.” The right model depends on your organization’s size, maturity, resources, and risk profile.
| CSaaS | In-House | |
|---|---|---|
| Upfront cost | Low (subscription-based) | High (infrastructure, hiring, tools) |
| Time to protection | Weeks | Months to years |
| 24/7 coverage | Included | Requires significant staffing |
| Expertise depth | Broad, across many clients | Deep, specific to your environment |
| Customization | Moderate | High |
| Compliance control | Shared with the provider | Full internal control |
| Scalability | Flexible, scales with subscription | Requires new hires and infrastructure |
| Talent dependency | On the provider’s team | On your own hiring and retention |
CSaaS makes the most sense when:
- You don’t have a dedicated internal security team and need protection now
- Your budget doesn’t support building and staffing a SOC
- You’re growing rapidly and need security that scales automatically
- You’re in a highly regulated industry and need compliance documentation support
- You want 24/7 coverage without the cost of shift staffing
In-house security makes more sense when:
- You operate at a scale where internal investment is justified (typically a large enterprise)
- You have strict data sovereignty requirements that prevent third-party access
- Your compliance environment requires full internal control over all security operations
- You already have a mature, well-staffed security function that doesn’t need external support
Key Benefits of Cybersecurity as a Service
Immediate access to expertise
- Building an internal team with the depth and breadth of a specialized CSaaS provider takes years. With CSaaS, that expertise is available immediately, including analysts who have investigated hundreds of incidents, threat hunters who know current attacker techniques, and compliance specialists who understand your regulatory environment.
Cost predictability
- CSaaS converts unpredictable security costs (a breach response can cost millions; a key hire leaving can disrupt your entire program) into a predictable monthly subscription. This makes security budgeting far more manageable, especially for organizations where finance and security leadership need to plan years ahead.
24/7 protection without shift staffing
- Cyber threats never sleep. The majority of ransomware attacks are triggered after business hours, during your typical shiftless times. With CSaaS, you get 24/7 security without staffing a graveyard shift at your company.
Faster threat detection and response
- CSaaS providers typically measure their detection and response times in minutes to hours rather than the industry average dwell time of weeks. Faster detection directly reduces the damage attackers can cause between initial access and containment.
Scalability
- Whether you’re adding 50 employees, migrating to a new cloud platform, or acquiring another company, CSaaS scales with your environment without requiring parallel investment in security headcount and tooling.
Staying current
- The threat landscape changes and develops all the time. CSaaS vendors spend the funds and time required to keep themselves up to date on new attack methodologies, up-to-date software, and increasing compliance issues, which you will benefit from as part of your subscription fee.
Who Needs CSaaS?
CSaaS is particularly relevant to businesses seeking enhanced cybersecurity capabilities without the need to build significant internal security teams.
1. Small and Medium-Sized Businesses (SMBs)
Due to a limited budget, most SMBs do not have a full security team but are susceptible to many of the same cybersecurity threats as large organizations. CSaaS offers them enterprise-grade security, monitoring, and expertise without the need for significant investment.
2. Fast-Growing Companies
As companies enter a growth phase, adopt cloud migration, and undergo digital transformation, they often find that internal security measures cannot cope. CSaaS offers a flexible option for security needs that can scale in line with business growth.
3. Regulated Industries
Industries that are subject to strict compliance standards, for example, Healthcare, Finance, Legal, Retail, and more, can benefit significantly from CSaaS. HIPAA, GDPR, PCI DSS, SOC 2, and others are easier to comply with when you are able to gain external support for monitoring and reporting.
4. Companies That Have Experienced a Breach
Often the need for an outsourced security team comes to light after a cyber-attack has exposed weaknesses in existing defenses. An external security provider can implement a plan of action that not only strengthens existing defenses and improves monitoring but also limits future risks.
5. Enterprises Experiencing Gaps
Even large companies can make use of CSaaS for services where their internal teams do not have expertise, for example, threat intelligence, dark web monitoring, penetration testing, or MDR.
Common Challenges and How to Address Them
- CSaaS can introduce operational complications, so organizations should understand key risks early to structure engagements effectively.
- Loss of direct control can be managed by setting clear escalation paths, maintaining internal oversight, and defining provider authority in contracts.
- Data privacy risks require reviewing what data is collected, how it is stored, retention policies, and compliance with regulations like GDPR and breach response obligations.
- Integration challenges may arise with legacy systems or custom tools, so running a proof of concept and confirming compatibility is essential.
- Alert fatigue from false positives should be addressed by evaluating detection quality, tuning methods, and SLAs for investigation and response.
- Vendor lock-in can be reduced by choosing providers that use open standards, avoid proprietary formats, and offer flexible exit terms.
How To Choose a CSaaS Provider
- Have a clear vision of what you’re looking for (SOC coverage, compliance support, vulnerability management, or threat intelligence) in order to easily weed out inappropriate vendors.
- Evaluate based on their detection and response capabilities above all else, with an understanding of their 24×7 analyst capability, analyst escalation, and incident response time SLAs (as opposed to just what tools the vendor can make available).
- Analyze the quality of their threat intelligence, taking into account their internal research capabilities, whether they collect intelligence from the dark web, and whether their intelligence is shared with all their clients.
- Prioritize a vendor with experience in your vertical, as security requirements and related regulatory burdens can differ widely.
- When speaking with references, ask them about actual security incident response time, the frequency of their false positive alerts, and how they communicate during security incidents.
- Closely examine all contracts for specific SLAs, data protection clauses, breach notification clauses, and lock-in potential.
Conclusion
Cybersecurity as a Service has moved from a niche option to a mainstream approach, and for good reason. The combination of an exploding threat landscape, a severe talent shortage, and the sheer cost of building effective security programs internally has made the outsourced model the most practical choice for the majority of organizations.
But CSaaS isn’t a switch you flip and forget about. It’s a partnership that requires clear requirements, careful vendor selection, and ongoing governance to deliver real protection. The organizations that get the most from CSaaS are the ones who approach it strategically: defining what they need, choosing providers with proven capability in those areas, and maintaining internal oversight of the program even as they outsource the operational work.
The other thing to keep in mind: most CSaaS programs still have a blind spot when it comes to the dark web. The threats that start there, credential listings, IAB auctions, ransomware targeting discussions, are invisible to tools focused purely on your internal environment. Making sure your security program has visibility into what’s happening outside your perimeter, not just inside it, is the difference between a security posture that’s reactive and one that’s genuinely ahead of the threat.



