Most people imagine a cyberattack as something dramatic. A hacker breaking through firewalls. An alert flashes on a screen. Someone is noticing something is wrong.
The reality is far quieter than that.
Infostealer malware sits silently on an infected device, methodically copying everything it can find, and then disappears without triggering a single alarm. The stolen data gets packaged into a file, uploaded to a criminal marketplace, and sold to the highest bidder within 48 hours.
That file is called a stealer log.
And right now, they are the primary fuel behind ransomware attacks, account takeovers, and corporate breaches happening around the world.
What Are Stealer Logs?
A stealer log is simply a collected bundle of data, put together by infostealer malware once it has already successfully compromised a device. It includes everything that the stealer was able to scrape from a given infected device, presented in a clean, easily searchable file format that criminals will buy and use immediately.
This data is essentially a full picture of a victim’s life online, at the point the malware has already made its way into their machine. From the active login sessions, password database, and credit card information through to the browser history, cryptocurrency wallet keys, and system information, it all comes bundled together and ready to be exploited.
Where traditional data breaches rely on hacking into company servers from the outside in order to extract data, a stealer log comes from within the device itself, and consequently, they are usually more up-to-date, more detailed, and more damaging than standard breach data.
In 2025, infostealer malware was responsible for the theft of 1.8 billion credentials, and log volumes available on top dark web markets have now grown by 670% since 2021. This isn’t a niche threat; it’s one of the fastest-growing forms of cybercrime currently underway.
What Exactly Is Inside a Stealer Log?
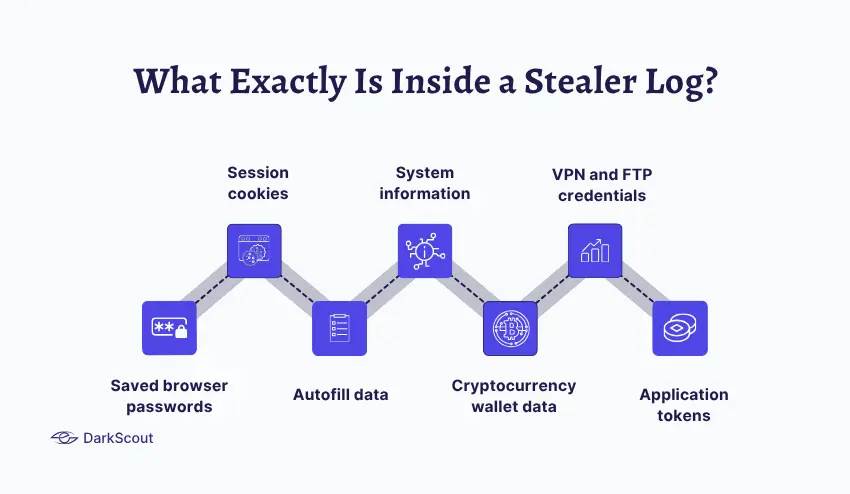
The contents of a stealer log go far beyond a simple list of usernames and passwords. Here is what a typical log contains:
- Saved browser passwords. Every password is stored in Chrome, Firefox, Edge, or any other browser on the infected device. This includes personal accounts, work accounts, banking portals, and anything else the user has ever logged into and chosen to save.
- Session cookies. This is one of the most dangerous elements. Session cookies are the tokens that keep you logged into websites after you authenticate. An attacker who imports a valid session cookie into their browser can access an account as if they were you, without needing to know the password and without triggering MFA prompts.
- Autofill data. Names, home addresses, phone numbers, dates of birth, and payment card details stored in browser autofill.
- System information. The device’s IP address, operating system, installed software, and hardware fingerprint. This helps attackers understand what they have access to and plan their next move.
- Cryptocurrency wallet data. Wallet addresses, seed phrases, and private keys for any cryptocurrency stored on the device.
- VPN and FTP credentials. Login details for remote access tools and file transfer systems, which can provide direct access to corporate networks.
- Application tokens. Access tokens for platforms like Slack, Discord, GitHub, and cloud services, which can be used to impersonate the user within those platforms.
A stealer log is not just a file. It is the full memory of a stolen identity, structured and ready for exploitation.
How Infostealer Malware Works
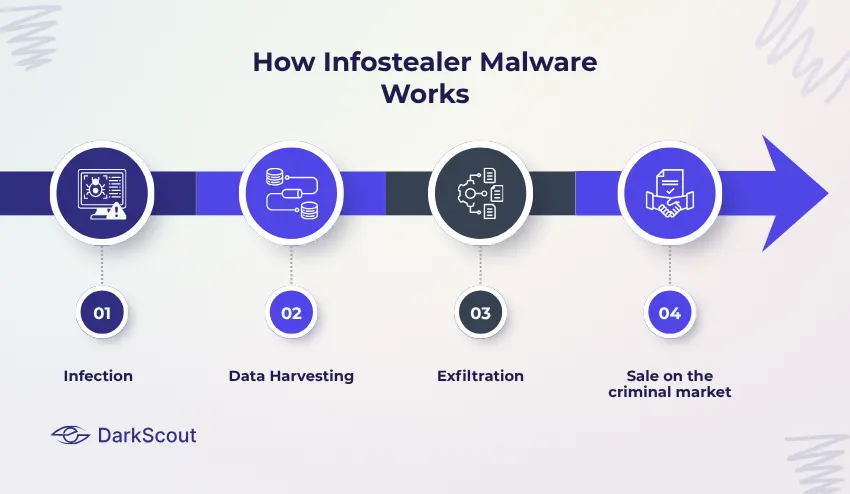
Now you know what stealer logs are; it’s time to look at how they are created. This is done in an organised, highly automated, and nearly invisible process:
- Infection
The infection of the device is one of the ways a victim could become infected. By far the most popular one is fake/cracked software. The victim downloaded something that looked like a free cracked application, game cheat, or piracy tool; the pirated tool worked perfectly fine while the infostealer ran in the background.
Some other, equally popular ways include phishing emails with infected attachments, fake updates for a browser that pop up on infected websites, and malicious ads (known as malvertising). According to IBM, phishing emails carrying infostealers increased by 84% year on year in 2024.
- Data Harvesting
Once it’s on the device, the malware starts collecting data from browser credential stores, system password managers, active session tokens, and application data. It does it silently and usually takes no longer than several minutes.
The malware is not locking up any files or demanding ransoms by displaying a ransom note; the victim thinks he is using their normal machine.
- Exfiltration
Collected data is being bundled into the stealer log file and transmitted to a Command-and-Control server belonging to attackers, where it will be neatly arranged, timestamped with the country and information about the machine, and put up for sale.
- Sale on the criminal market
Logs are being put on sale for around 24 to 48 hours after they are created on some of the most popular markets for credentials like 2easy or the Russian Market, where ‘freshness’ of the log is of the utmost importance, and each log can sell for $5 to $50, with Enterprise access to VPN or SSO selling for hundreds of dollars.
The time that all this takes can still be shorter than a security team’s morning threat briefing.
The Malware Families Behind Stealer Logs
Several infostealer variants dominate the market. Understanding which ones are most active helps explain the scale of the problem.
- Lumma (LummaC2). The most dominant infostealer on dark web forums throughout 2024 and into 2025. Lumma operates as Malware-as-a-Service, meaning anyone can license it for a monthly fee without any technical expertise. In May 2025, the US Department of Justice and Microsoft jointly disrupted Lumma’s infrastructure, seizing domains and taking down over 2,300 associated public-facing sites. The FBI estimates Lumma was tied to at least 1.7 million fraud cases. Despite the takedown, variants remain active.
- RedLine. One of the longest-running infostealers, designed to harvest browser data, system information, and cryptocurrency wallets. It has been widely used in attacks across industries.
- Vidar. Spreads through phishing emails, cracked software, and even fake games. A 2025 campaign used a fake game called PirateFi to deliver the payload. Once deployed, Vidar compiles stolen data into structured logs organised by platform and credential type.
- RisePro. One of the fastest-growing infostealers in recent years. Written in C++ and designed to steal login credentials, browser cookies, and credit card data at scale.
- Raccoon. A popular Malware-as-a-Service variant that became widely used due to its ease of deployment and broad data collection capabilities.
Why Stealer Logs Are More Dangerous Than Regular Breaches
Traditional data breaches expose password hashes or older credentials. Stealer logs are fundamentally different, and significantly more dangerous for several reasons.
- They bypass MFA. This is the most alarming aspect. When an attacker uses a stolen session cookie from a stealer log, they do not need to authenticate at all. They import the cookie into their browser, and they are already logged in, with an active session that looks entirely legitimate. Two-factor authentication provides no protection against this.
- The data is fresh. Stealer logs contain credentials and session tokens from the moment of infection. Unlike breach dumps from years ago, these credentials are active and valid. Session tokens from infections within the past 48 hours command premium prices on dark web markets specifically because they have not yet expired.
- They contain corporate access. Analysis of 19.6 million stealer logs found that 46% contained corporate credentials. 30% of compromised systems were enterprise-licensed. 46% of systems with corporate credentials were non-managed devices, where security controls are often far weaker.
An employee who gets infected at home, on a personal laptop they also use for work, can expose their entire organisation’s systems through a single stealer log. - They connect directly to ransomware. According to Verizon’s 2025 DBIR, 54% of ransomware victims had their domain credentials appear in stealer logs before the ransomware attack. In many documented cases, ransomware deployment followed within 48 hours of the credentials appearing on the marketplace.
Stealer logs are not just a credential theft problem. They are frequently the first step in a ransomware attack.
Real-World Examples
Samsung (2025). A contractor’s credentials for the Samsung support site were stolen through infostealer malware and remained unnoticed on a dark web forum. When those credentials were eventually used, the attacker accessed Samsung’s support database and extracted 270,000 customer support tickets. Samsung itself was not directly hacked. A contractor’s stolen credentials from a stealer log were all it took.
Telefónica (2025). HellCat ransomware actors obtained credentials from over 500 Telefónica employees through infostealer malware, including those with administrative privileges. Using this access, they conducted extensive reconnaissance and exfiltrated a list of 24,000 employee names and emails, 5,000 internal files, and approximately half a million internal issue summaries.
CircleCI (2023). A stolen session cookie from an engineer’s device gave attackers access to production systems. This was not a password breach. The attacker bypassed all authentication controls using a valid active session harvested by infostealer malware.
How to Protect Yourself and Your Organisation
The defences against stealer logs require both individual habits and organisational controls.
For Individuals
- Do not save passwords in your browser. Browser credential stores are the primary target for infostealer malware. Use a dedicated password manager with its own encryption instead.
- Be careful about what you download. Fake software, game cracks, and pirated tools are the most common infection vector. If you did not get it from the official source, treat it as suspicious.
- Keep software updated. Many infostealer campaigns exploit unpatched vulnerabilities in browsers and operating systems to gain access. Regular updates close those doors.
- Check if your credentials have been exposed. DarkScout’s free email scan checks whether your email and associated credentials have appeared in known breach data, including stealer log dumps.
For Organisations
- Monitor for exposed credentials continuously. The window between a stealer log appearing on dark web markets and an attacker using it can be as short as 48 hours. DarkScout’s dark web monitoring watches criminal forums and marketplaces around the clock, alerting you the moment credentials tied to your organisation appear.
- Enforce endpoint security on all devices. Behaviour-based endpoint detection tools can identify infostealer activity by watching for unusual data access and exfiltration patterns rather than relying on known malware signatures.
- Implement strict policies on personal devices. Employees using personal devices for work create a significant risk. Corporate credentials saved on a personal laptop with weaker security controls are a prime target for infostealer malware.
- Use phishing-resistant authentication. Session-based MFA bypass is one of the most dangerous capabilities stealer logs enable. Hardware security keys and FIDO2-based authentication methods are significantly more resistant to this kind of attack than app-based or SMS codes.
- Rotate credentials immediately after any suspected exposure. Stolen credentials and session tokens become worthless the moment they are invalidated. Fast response is critical.
For a deeper look at how stolen credentials flow through criminal networks and what you can do to stay ahead of them, our guide on dark web monitoring covers the broader picture. And if you want to understand how stealer logs connect to account takeover attacks, our blog on credential stuffing explains exactly how attackers weaponise the data from these logs.
The Bottom Line
Stealer logs have quietly become one of the most significant threats in cybersecurity. They are cheap to produce, easy to distribute, and devastatingly effective because they bypass the controls most organisations rely on.
The data they contain does not just sit there. It flows directly into ransomware attacks, account takeovers, and corporate breaches. More than half of ransomware victims in 2025 had their credentials exposed in stealer logs before the attack. The credential exposure was not the attack itself. It was the warning sign that most organisations had no visibility into.
The difference between organisations that catch this early and those that discover it after a breach is monitoring. Knowing your credentials are circulating on dark web markets while there is still time to rotate them is the entire value proposition.



