Cybercriminals don’t hide their plans from each other. They discuss targets, sell stolen data, trade credentials, and recruit affiliates openly, just on parts of the internet most organizations can’t see.
That’s the dark web. And for security teams, flying blind to what’s happening there is no longer acceptable.
OSINT dark web tools give analysts the ability to monitor those hidden environments, gather intelligence on emerging threats, and act before an attack reaches their organization. Whether you’re a SOC analyst, a threat intelligence professional, or a business owner trying to understand your exposure, this guide covers everything you need to know: what OSINT dark web tools are, why they matter, which ones are worth knowing, and how to build a safe, effective workflow around them.
What Are OSINT Dark Web Tools?
OSINT is Open Source Intelligence, which means the collection and analysis of data from publicly available sources. Traditional OSINT typically includes data obtained from surface web resources such as company websites, social media networks, news outlets, and public government data.
OSINT dark web tools apply the OSINT principles to the deep web, where they focus on .onion sites, Tor networks, darknet marketplaces, password-protected websites, paste sites, and private channels that can only be accessed by a Tor-based browser and are not indexed by normal search engines.
These tools help security professionals do several things:
- Monitor dark web markets and forums for company or brand names as well as executive mentions.
- Search for stolen credentials, leaked databases, and sensitive data available on dark markets.
- Monitor for malicious actor activity, ransom group discussions, and threat planning.
- Conduct investigations into criminal activity and link up malicious actors.
- Collect data that can be used to conduct incident responses and hunt threats.
To make a distinction in this regard, OSINT dark web tools don’t generate data from scratch; rather, they are methods for an analyst to be safely provided with data that is already being released in unseen regions.
OSINT vs DARKINT: Understanding the Difference
Before we dig any deeper, it’s useful to quickly distinguish a concept that you hear about a lot in the world of threat intelligence:
OSINT – or Open Source Intelligence, involves information gained from openly accessible, publicly available resources – content on the surface web, public documents, social media sites, and essentially anything that does not require any specialized access or equipment to view.
DARKINT – or Dark Web Intelligence, is a specific category of threat intelligence specifically targeting the underlying, hidden networks like the Tor Network, I2P, and ZeroNet, and others of that ilk. DARKINT requires the use of specific equipment and techniques that are designed to facilitate safe access to dark websites without flagging your activity, and is far removed from that of using a regular search engine.
The relevance of the distinction to you and your team lies in its practical application. Many of the tools currently being advertised as “dark web OSINT” are actually DARKINT tools, as they not only parse public data, but will also access dark web content directly via dark web searching or by scraping hidden services and indexing .onion content directly from within the network. Being aware of the distinction between an OSINT and a DARKINT tool helps you to decide the sort of training, procedures, and even technology you’ll need before using it.
Most security teams will likely use both OSINT tools to monitor the surface and deep web, while still keeping the use of DARKINT tools for when the coverage they offer is needed.
Why Organizations Need Dark Web OSINT
Most cyberattacks don’t come out of nowhere. Before ransomware deploys, before credentials get used for account takeovers, before a phishing campaign hits your inbox: there’s usually activity on the dark web that preceded it.
Initial Access Brokers advertise access to your network on forums. Stealer logs containing your employees’ passwords get posted to darknet markets. Ransomware groups discuss targets before they strike. Data stolen from a third-party vendor you work with gets listed for sale weeks before you find out about the breach.
Dark web OSINT gives organizations a chance to see those signals before they become incidents.
Here are the specific use cases that make dark web OSINT valuable in 2026:
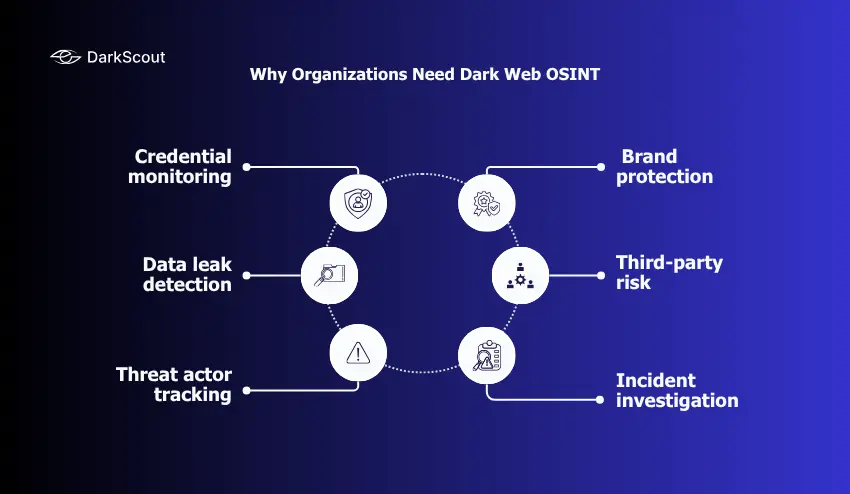
1. Credential monitoring
Are your organization’s credentials present within breach dumps, stealer logs, or credential databases that are for sale on dark web forums? Stolen credentials represent the largest source of entry for both ransomware and account takeovers.
2. Data leak detection
Identifying whether proprietary documents, customer data, financial records, or source code have been posted or sold on dark web platforms often occurs before the originating breach has even been discovered.
3. Threat actor tracking
Monitoring the activity of specific threat groups, ransomware operators, or Initial Access Brokers to understand their targeting patterns, tools, and upcoming campaigns.
4. Brand protection
Detect counterfeit goods or domains, impostors, and fakes using your company’s name and branding on dark web marketplaces and forums.
5. Third-party risk
Identifying exposure that originates from suppliers, vendors, or partners whose data may have been compromised and is now available for purchase on darknet markets, putting your organization at risk by association.
6. Incident investigation
During or after a breach, dark web OSINT helps determine what was stolen, where it went, and who has it, critical information for regulatory notification, legal response, and understanding attacker attribution.
Overall Context is Critical Here As Well: As of 2026, researchers had logged more than 9,000 victim postings on ransomware leak sites. More than 2.7 million individuals visited the dark web daily. The criminal underground is sophisticated, operational, and invisible to most organizations without the necessary tools.
Categories of OSINT Dark Web Tools
Dark web OSINT tools aren’t all the same. They serve different functions, and a mature threat intelligence program typically combines several categories. Here’s how to think about them:

1. Access and Anonymization Tools
Before it’s possible to even research the dark web, it needs to be safely accessed. These are fundamental tools that allow you to anonymously browse .onion services.
Standard access is through the Tor browser, a piece of software that uses Tor’s distributed network to route traffic through several encrypted nodes, ensuring that your connection is anonymous. For more investigative work, it’s vital that these tools are used in combination with a reputable VPN, and run from a disposable operating system like Tails or Whonix, and hardware or Virtual machines that are not tied to an organization or your personal life.
Skipping these steps creates serious operational security (OPSEC) risks. Most documented cases of investigators being identified trace back to OPSEC failures, not flaws in the tools themselves.
2. Dark Web Search Engines
Standard search engines don’t index .onion content. Dark web search engines fill that gap, crawling hidden services and making them searchable.
Ahmia is one of the most popular and legitimate dark web search engines; it indexes .onion websites without illegally linked content and can be accessed directly via the surface or dark web through Tor.
Haystak and Kilos offer more advanced searching capabilities than Ahmia; they can filter results through use of fields and index content more deeply. These are more commonly used by researchers needing very specific and niche results from the dark web.
Torch is one of the oldest dark web search engines, with a large index that covers a broad range of .onion sites.
3, Threat Intelligence and Monitoring Platforms
These are the tools that go beyond search, providing continuous monitoring, automated alerting, and structured intelligence across dark web environments. For most enterprise security teams, this category is where most of the operational value lives.
Intelligence X is a search engine and archival platform that searches across dark web sources, data breach dumps, public records, and historical datasets using specific identifiers like email addresses, domains, IP addresses, and cryptocurrency wallet addresses. It’s particularly useful for breach investigation and tracking specific entities across multiple dark web sources.
DarkOwl provides tools that collect and offer real-time access to dark web information. Their platform accesses Tor, I2P, and ZeroNet in addition to forums, paste sites, and ransomware leak sites. This gives investigators structured access to an up-to-date dark net database through API feeds that can be ingested directly into an organization’s SIEM and SOAR.
Maltego is a graph-based investigation platform that visually shows the relationships between pieces of information: email addresses, social media profiles, IP addresses, domain names, and dark web personas. This can be incredibly useful when tracking attribution from the dark web across to multiple other platforms.
4. Breach Monitoring Tools
These tools are specialized to identify whether organizational credentials and sensitive data have appeared on the dark web, often due to a data breach or from infostealer malware:
Have I Been Pwned? (HIBP) It is the most popular free credential monitoring tool, where individuals or organizations can input a specific email address and receive an alert if that email address has been involved in a known data breach. While it’s extremely useful as an initial tool, HIBP only scans breaches that are known and available for inspection.
LeakOSINT is a Telegram bot that monitors dark web sources and notifies when a new data breach has occurred; this can be a good real-time alerting tool.
Stealer log marketplaces (monitored indirectly) contain credentials, session tokens, and browsing data harvested by infostealer malware from infected devices. Professional monitoring services track these markets and alert organizations when their data appears.
5. Cryptocurrency and Blockchain Analysis Tools
Cryptocurrency represents the payment layer for much of the dark web economy. These tools are invaluable for tracing financial activity and connecting cryptocurrency wallet addresses to specific users or organizations.
The user-friendly, low-cost tool Breadcrumbs allows you to trace cryptocurrency transactions and map wallet addresses to exchanges, but more sophisticated enterprise tools like Chainalysis and Elliptic are commonly used by security and law enforcement teams for their comprehensive analysis capabilities.
6. Crawler and Automation Tools
To quickly obtain large amounts of information from the dark web in a way that can be easily ingested, automated tools are key.
TorCrawl.py is an open-source tool that can index the contents of .onion sites, allowing for easier programmatic analysis of large quantities of data.
DeepDarkCTI is a tool designed for gathering and analyzing dark web threat intelligence, tailored for use by CTI teams and SOC analysts, and can be integrated directly into other security tooling.
Robin is an AI-driven tool that allows analysts to generate highly targeted search terms using large language models to increase relevance in dark web searches and help analyze the large amounts of data from those searches. It supports multiple LLM backends and has a user-friendly web interface.
Top OSINT Dark Web Tools in 2026
Here’s a consolidated reference of the most relevant tools for dark web OSINT work in 2026:
| Tool | Category | Best For |
|---|---|---|
| Tor Browser | Access | Secure .onion browsing |
| Tails OS | Access/OPSEC | Non-persistent, anonymous investigative environment |
| Ahmia | Search | General .onion search, surface web accessible |
| Haystak | Search | Advanced dark web search with fielded filters |
| Intelligence X | Intelligence Platform | Cross-source breach and entity investigation |
| DarkOwl | Intelligence Platform | Enterprise darknet monitoring with SIEM/SOAR integration |
| Maltego | Investigation/Attribution | Relationship mapping between threat actors and entities |
| Have I Been Pwned | Credential Monitoring | Quick credential exposure check |
| LeakOSINT | Credential Monitoring | Real-time breach alerting via Telegram |
| Breadcrumbs | Blockchain Analysis | Cryptocurrency transaction tracing |
| TorCrawl.py | Automation | Programmatic .onion data collection |
| Robin | Automation/AI | AI-assisted dark web investigation and reporting |
| Shodan | Network Intelligence | Exposed device discovery and infrastructure mapping |
No single tool covers everything. Effective dark web OSINT programs layer access tools, search engines, monitoring platforms, and investigation tools based on the specific intelligence requirements of the team.
How to Conduct a Dark Web OSINT Investigation Safely
Dark web investigations require a structured workflow. The technical risks are real: malware-laden sites, honeypots, and adversaries who actively monitor for investigators. The legal risks are equally real if the wrong content is accessed or handled improperly.
Here’s a step-by-step approach that balances operational effectiveness with safety:
Step 1: Define your intelligence requirement
What are you looking for and why? Before ever launching the Tor browser, define the scope and objective of your investigation. Are you checking for credentials exposed, investigating a threat actor group, or monitoring brand mentions? Knowing this will avoid the temptation of aimless exploration that increases the risk and adds no intelligence.
Step 2: Set up an isolated environment
Never perform a dark web investigation using your own personal, corporate, or work device with access to your regular accounts. Instead, use a dedicated, and preferably non-persistent, device or VM such as the TAILS or Whonix operating systems. If you do land on a malware-laden site or honeypot, the damage is limited to the disposable operating system, not your primary environment.
Step 3: Layer your anonymization
Route the Tor browser over a VPN (vpn then Tor). This not only prevents your ISP from knowing you are using Tor but also adds a layer of encryption before the traffic ever reaches the Tor network. Choose a non-logging VPN and consider using it in a multi-hop configuration if handling highly sensitive information.
Step 4: Start with passive, surface-accessible tools
Start your investigation by using already existing OSINT tools designed to access dark web data through secure interfaces such as Intelligence X, Have I Been Pwned, breach monitoring platforms, and threat intelligence services. They are a wealth of dark web data that does not require the OPSEC demands of using the Tor browser directly.
Step 5: Use dark web search engines for targeted queries
Once you have a need to use Tor, be specific. Use well-known dark web search engines such as Ahmia, Haystack, and Gigi to conduct precise queries rather than trawling through the listed sites, of which you have no information regarding their content or trustworthiness.
Step 6: Document everything methodically
Maintain a detailed investigation log of all activities, including queries used, sites visited, data discovered, how it was discovered, and the method used for discovery. This level of documentation will be crucial if you later need to refer to these logs for regulatory compliance (e.g., breach notification), legal action, or if referring the matter to law enforcement.
Step 7: Handle found data carefully
If you find data belonging to your organization on the dark web (e.g., stolen credentials or proprietary documents), treat it as sensitive evidence. Only download what is absolutely necessary to prove or disprove the compromise, and familiarize yourself with the legal statutes governing your jurisdiction in relation to possessing this type of data. It may be wise to consult with legal counsel if the finding is of significant interest.
Step 8: Integrate findings into your security workflow
Having intelligence that exists only in a documented investigation report, doing nothing. Feed findings into password reset workflows, mandate multi-factor authentication if compromise of credentials is discovered, and refine threat detection signatures to block access based on new adversary tactics observed in dark web investigations.
Legal and Ethical Considerations
Dark web OSINT is fraught with potential legal and ethical issues that any practitioner should understand before commencing.
The legality is location-dependent. Browsing the dark web isn’t inherently illegal in most countries. What you do within it, however, may be illegal: browse illegal markets, download illegal data, or use illegal services. Researching security and performing these tasks does not shield you from legal prosecution under certain laws if you attempt to download or consume a certain type of content.
Handling the data you find is also a risk. If, while investigating, you discover personal data stolen from users or from your organization, the way you handle it could still expose you to privacy regulation issues under GDPR, HIPAA, or any similar regulations. The normal practice here is to document what was found and, where possible, not download it in full, and notify affected parties through the proper channels.
Authority is an issue. If working on behalf of an organization to find something on the dark web, you must have explicit written authorization to do so. If searching for a third party, even one considered a threat actor, you must understand the limitations and boundaries of your authority and where you are legally restricted from going.
Ethics are important independent of the law. Some activities, while technically legal on the dark web, are ethically complex. You should have clear organizational policies on what kind of content analysts are allowed to encounter, and what to do when child abuse material, for instance, is found. It should be immediately reported and not downloaded or further explored.
For most organizations, the way forward is professional dark web monitoring services, which handle the access layer themselves and provide you with the intelligence without exposing internal analysts.
How Dark Web OSINT Fits Into Your Security Program
Dark web OSINT doesn’t replace other security capabilities. It adds an intelligence layer that makes everything else more effective.
Here’s how it connects to the broader security program:
Threat intelligence – Dark web OSINT provides specific, actionable information about who is targeting your industry, their capabilities, and their motivations. Generic threat intel becomes context-rich regarding what risks your organization may face.
Vulnerability management – Being able to identify that a particular software vulnerability is being actively discussed and exploited on Dark Web forums and have the ability to correlate it with your use of the vulnerable software allows you to prioritize patches and remediation efforts much more efficiently.
Incident Response – In the event of an active security incident, having Dark Web OSINT will assist your IR team in quickly understanding the breadth of an attack – what data has been exfiltrated, where it has gone, if it is listed for sale on the dark web, or if a ransomware threat actor intends to leak it. The intelligence gathered can further guide your legal notification timeline and negotiation strategy.
Risk assessment – Details from your IAB listing, known credentials, and dark web conversations referencing your organization would feed into your cybersecurity risk assessment process directly to show you your real-world security risk.
Ransomware prevention – Understanding the threat landscape and how dark web ransomware actors conduct their business, as well as how initial access brokers are advertising network access for sale and the typical timeline and methodology that ransomware groups use for leaking data, informs effective defenses against such threats.
Brand protection – Dark web monitoring for impersonation, counterfeit products, and fraudulent use of your brand name gives your legal and communications teams early warning to act before reputational damage spreads.
Conclusion
The dark web is where the modern threat economy operates. Credentials get sold, network access gets auctioned, ransomware affiliates get recruited, and your organization’s data may already be circulating in marketplaces you’ve never seen.
OSINT dark web tools give security teams the visibility to operate in that environment: to find threats before they become attacks, to detect exposure before it gets exploited, and to gather intelligence that makes every other security control more effective.
Building that capability doesn’t require every analyst to become a dark web expert. It requires the right combination of tools, a clear workflow, proper OPSEC, and, for most organizations, a professional monitoring layer that handles continuous surveillance so your team can focus on acting on the intelligence rather than collecting it.
If you want to understand your current dark web exposure, DarkScout’s free email scan is a fast first step: it checks immediately whether your organization’s addresses have appeared in known breach data. For ongoing intelligence, DarkScout’s Dark Monitoring and Darknet Threat Assessment services provide the continuous coverage that most organizations need without requiring internal teams to manage the access layer themselves.