Most people assume that once a company is hacked, the stolen data disappears into a void. It does not.
Within hours of a breach, that data, your email, your password, your credit card number, is listed for sale on a darknet marketplace. These are fully functioning online stores, complete with product categories, vendor ratings, customer reviews, and buyer protection. They just happen to operate in the hidden corners of the internet, accessible only through specialized software, and they trade exclusively in stolen, illegal, or harmful goods.
In 2025, darknet marketplaces processed nearly $2.6 billion in transactions. Despite repeated law enforcement takedowns, the ecosystem does not shrink. It adapts. When one market falls, another absorbs its vendors and users within days. This is not a fringe threat. It is a mature, resilient criminal economy, and your data is one of its most traded commodities.
This guide explains what darknet marketplaces are, how they work, what is sold on them, and what you need to do to protect yourself.
What Is a Darknet Marketplace?
A darknet marketplace is a website that can only be accessed on the dark web and acts as a trading hub where people can purchase illegal goods and services such as stolen data, hacking tools, counterfeits, and illicit drugs.
They essentially mirror legal marketplaces online. This includes product listings, vendor accounts, consumer reviews, and product search functions, as well as dispute resolution services and potentially even loyalty programs and money-back guarantees. However, the important differentiating factors are where these services operate and from whom these services are bought/sold.
Quick definition: A darknet marketplace is an anonymous, Tor-based online store that enables criminals to buy and sell illegal goods and services using cryptocurrency, with built-in features to protect the anonymity of buyers, sellers, and administrators from law enforcement.
They are sometimes called dark web markets, dark markets, or DNMs. All of these terms refer to the same category of platform.
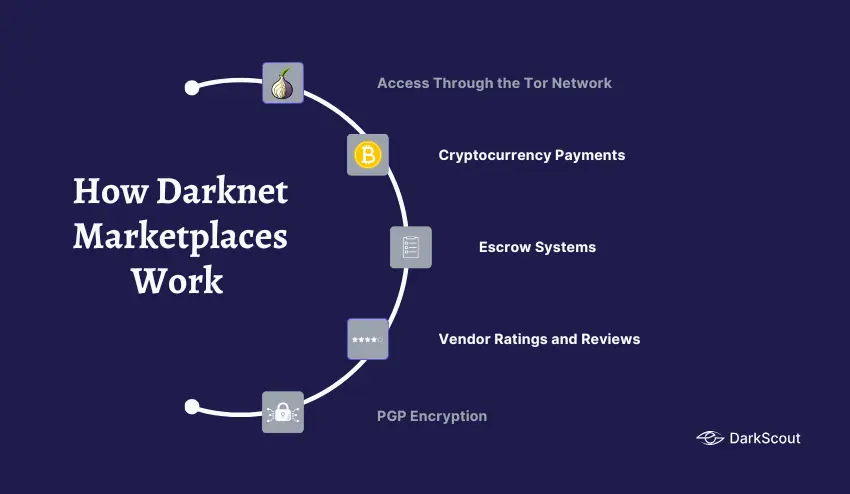
What separates them from surface web crime is the combination of three technologies: the Tor network for anonymity, cryptocurrency for untraceable payments, and end-to-end encryption for secure communications. Together, these three tools created an environment where criminal commerce could scale to billions of dollars in annual volume.
How Darknet Marketplaces Work
An understanding of how they work explains why they are so resilient and why the closure of a particular market never truly stops things.
1. Access Through the Tor Network
Darknet markets are hosted on the Tor network as hidden services and are only accessible through the Tor Browser. They do not have typical internet addresses but use .onion domains-long, random strings of characters, not indexable by any search engine-and whose addresses can change at short notice to evade seizure.
To access a market, users need the current .onion address for the market. They will often maintain multiple mirror links in case any single site goes down. Dedicated forums such as Dread act as directories for users to share working onion addresses and confirmed market URLs.
2. Cryptocurrency Payments
All transactions on a darknet market use cryptocurrency. Bitcoin was the original currency for darknet markets; however, due to its relatively traceable nature through blockchain analysis, many have transitioned to privacy-focused coins like Monero, which obscure transaction amounts, senders’ addresses, and recipients’ addresses by default.
The switch to Monero is a reaction to the capabilities of law enforcement. It is now very easy for the police to track Bitcoin transactions, and the increasing rise of companies such as Chainalysis, and the forensic power that their blockchain analysis gives them is such that it allows law enforcement to track any Bitcoin payment through even mixers.
3. Escrow Systems
Most trustworthy darknet markets include a way for buyers and sellers, with little reason to trust each other, to verify that they have both fulfilled their contractual obligations.
Buyers sending money to a darknet market submit the cryptocurrency, where the funds are held by the market administration in an escrow. The funds are then sent by the market administration to the vendor once the buyer has confirmed that the delivery was as expected. These are similar to the systems used on the site eBay, except that on darknet markets these are facilitating illegal transactions.
However, multi-signature escrow, requiring the agreement of both buyer and seller’s cryptographic keys to release funds, is now the most trusted means as this is very difficult for the administration of the market itself to steal, as they are known as an ‘exit scam’.
4. Vendor Ratings and Reviews
Like Amazon or Etsy, darknet markets rely on ratings and reviews to signal vendor reliability. Buyers leave feedback on product quality, shipping speed, and vendor communication. Vendors build reputations over time, with high ratings commanding premium prices and attracting more buyers.
This reputation system is what makes markets sticky. Vendors who have built strong ratings are reluctant to move platforms, and buyers gravitate toward established vendors with verified track records.
5. PGP Encryption
Most transactions between the buyers and the sellers are conducted through PGP encryption. This means that encrypted messages are passed between the two individuals concerning details about the product that they are buying or selling, and details concerning the shipping address. These messages cannot be read by administrators on the market or by any third party.
What Is Sold on Darknet Marketplaces?
The inventory of a typical darknet marketplace is broad. Understanding what is traded matters because it defines the downstream risk to individuals and organizations.
1. Drugs
Drugs consistently account for the majority of listings across all major darknet markets. Cannabis, MDMA, stimulants, opioids, and prescription medications dominate volume. According to Chainalysis data, drug-related flows accounted for most of the $2.6 billion in darknet marketplace activity in 2025.
2. Stolen Credentials
This is the category most directly relevant to cybersecurity. Stolen usernames and passwords from data breaches are sold in bulk, organized by service type: email accounts, streaming subscriptions, banking logins, corporate VPN credentials, and admin panel access.
Russian Market is the dominant darknet marketplace for stolen credentials in 2026. It specializes in stealer logs, bundles of harvested passwords, session cookies, and browser autofill data extracted from infected devices by infostealer malware. Credentials appear on the Russian Market within hours of being stolen from a victim’s device.
3. Stealer Logs
Stealer logs are packages of data harvested from a single infected device. A single log can contain hundreds of saved passwords, all browser cookies, autofill data, including addresses and card numbers, email credentials, and cryptocurrency wallet files.
These logs are sold as individual packages and in bulk. A fresh log from a corporate device connected to a company network can sell for significantly more than consumer device logs because of the potential for lateral movement into business systems.
4. Financial Fraud Tools
Stolen credit card data is traded on dedicated carding markets. BidenCash, one of the largest carding platforms, was seized by U.S. authorities in June 2025, having previously distributed millions of stolen card records through promotional data dumps. New carding markets have since absorbed its activity.
Other financial fraud tools include bank account logins with verified balances, PayPal and Venmo account access, and money transfer service credentials.
5. Hacking Tools and Services
Darknet markets and associated forums sell ready-made malware, ransomware kits, exploit code for known vulnerabilities, phishing kits, ClickFix builder tools, and access to compromised infrastructure.
Ransomware-as-a-Service (RaaS) operations recruit affiliates through dark web forums adjacent to marketplaces. Initial access brokers, criminals who specialize in breaching organizations and selling that access, list corporate network access on darknet markets alongside standard consumer credential listings.
6. Counterfeit Documents
Fake passports, driver’s licenses, national identity cards, and supporting documents are traded on most general-purpose darknet markets. These are used for identity fraud, account creation at financial institutions, and bypassing KYC verification systems.
7. Personal Identifiable Information
Full identity packages, known as fullz, bundle together a victim’s name, address, date of birth, Social Security number or equivalent national ID, and financial account details. These are used for synthetic identity fraud, loan fraud, and tax refund theft.
The History of Darknet Markets
Understanding how darknet markets evolved explains why taking them down does not eliminate them.
1. Silk Road (2011 to 2013): The First Market
Founded in February 2011 by Ross Ulbricht (pseudonym: Dread Pirate Roberts), Silk Road was the first large darknet market combining Tor anonymity with Bitcoin payments within a traditional e-commerce site appearance.
Over its lifespan (2011 – its closure by the FBI in October 2013) it processed sales totaling 9.5 million Bitcoins, which in 2013 values equaled approximately $1.2 billion. Ulbricht was arrested, tried, and convicted for two life sentences, but was pardoned by President Trump in January 2025 after 11 years of imprisonment.
Its closure, however, didn’t stop darknet trade; Silk Road was the proof of concept and was followed by similar enterprises.
2. AlphaBay and the Second Generation (2014 to 2017)
AlphaBay was launched in 2014, and had become ten times larger than Silk Road at the time of its takedown by Operation Bayonet, a combined raid by the FBI, DEA, and Europol, in 2017. AlphaBay was the largest dark web marketplace it’s time with 200,000+ users and 250,000+ listings.
An interesting covert operation also occurred with Operation Bayonet, where the Dutch National Police secretly ran the Hansa market for 27 days before closing it and gathering all of the buyer and vendor information. This allowed for the acquisition of all the users currently using the marketplace and was the basis of the arrests that occurred in many countries, and set the example for many modern dark web law enforcement methods.
3. Hydra: The Dark Web Empire (2015 to 2022)
Hydra was an increasingly significant Russian-language darknet market. The value of cryptocurrency passed through the market between 2015 and 2022 was $5.2bn, and it is thought that at its peak, 80% of the world’s darknet market traffic passed through the marketplace.
However, Hydra was more than a simple darknet market; it was a whole black market economy that included services like money laundering, crypto mixing, and delivery via the dead-drop system (a service that provided buyers with map coordinates and demanded they navigate to a specified location to retrieve their package).
In April 2022, the German Federal Police shut the Hydra servers down, and the marketplace was taken offline after the DOJ, DEA, and the IRS-CI were involved in an investigation that led to them seizing approximately $25 million in cryptocurrency. The closure of Hydra created a void on the dark net market.
4. The Post-Hydra Fragmentation (2022 to 2024)
No single market gained the prominence that Hydra enjoyed once it was gone; instead, competing successor markets scrambled for displaced vendors and customers. The three prominent Russian-language successes of this era were OMG!OMG!, BlackSprut and Mega. In English-language markets, the most significant success was Abacus which rapidly expanded and became, at over 40,000 listings, the largest Bitcoin-enabled darknet market in the West.
5. The Current Landscape (2025 to 2026)
2025 continued to be the year of disruption, by both law enforcement and the markets themselves.
May 2025-Operation RapTor arrested 270 suspects in ten countries, seized more than 200 million USD in cryptocurrency, cash, and illicit goods, and shuttered Incognito Market, the largest single dark net market takedown of its kind.
June 2025-Europol took the lead in a raid that took down Archetyp Market, the longest-running dark net drug market on the network (over five years), the market having amassed more than 600,000 registered users and over 250 million EUR in transactions, under Operation Deep Sentinel.
Mid-2025-The once dominant Abacus Market ceased operations, most analysts believing this to be an exit scam and that operators had made off with all escrowed funds. BidenCash, the premier carding marketplace on the dark net, was seized by US authorities in June 2025.
By mid-2026, TorZon would become the primary Abacus successor in the Western-facing portion of the dark net market universe, absorbing much of its displaced vendor and customer base as it rapidly expands. The Russian Market would still be considered the top marketplace for stolen credentials and stealer log trading worldwide.
Active Darknet Marketplaces in 2026
This is not an access guide. It is an intelligence overview for understanding what security teams and individuals are up against.
1. TorZon Market
TorZon is currently the most prolific darknet market, rising in 2025 after integrating vendors from the abandoned Abacus Market and other closed-down markets. There are currently more than 15,000 items available on the market, varying from illegal substances and data to false documents and other means of deception. It is currently regarded as the premier Western darknet market following the closure of Abacus Market in July 2025 and as an important player in the supply network between markets.
2. Russian Market
Russian Market has been identified as the leading darknet market for stolen credentials in 2026. The market primarily lists stolen logs and corporate access data and will feature the sale of credentials taken from victims within hours of being stolen. It is regularly screened by security teams as it indicates the success of an organization being targeted by an infostealer attack with the quickest response.
3. WeTheNorth
A Canadian-focused darknet market that successfully navigated the market chaos from 2024 to 2025 and operates consistently as a regional alternative to the general-purpose markets.
4. STYX Market
STYX Market is identified as a niche, fraudulent-focused market. STYX has previously specialized in the sale of financial fraud instruments, identity documents, and account takeover (ATO) services.
5. Dread
Not a marketplace itself, Dread is a Reddit-style forum that functions as the central hub for darknet market discussion. Vendors advertise on it, buyers post reviews, scam alerts circulate, and market shutdowns are announced. Monitoring Dread provides early warning of market closures, law enforcement actions, and emerging fraud campaigns.
How Law Enforcement Fights Back
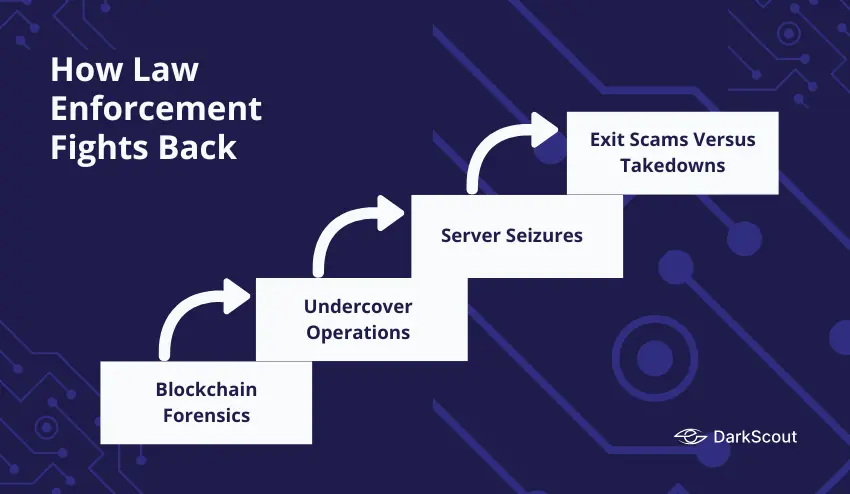
Law enforcement has developed sophisticated and effective methods for infiltrating and dismantling darknet markets. Understanding these methods also explains why darknet markets continue to persist despite repeated takedowns.
1. Blockchain Forensics
Every cryptocurrency transaction leaves a permanent record on the blockchain. Blockchain intelligence firms like Chainalysis and TRM Labs help law enforcement trace the flow of funds from darknet marketplaces through mixer services, exchanges, and ultimately to cash-out points where real identities must be revealed.
When Hydra Market was seized, on-chain analysis revealed the full scope of its revenue and identified the network of exchanges that had processed Hydra proceeds. This same analysis supported enforcement actions against those exchanges.
2. Undercover Operations
Law enforcement agencies establish vendor accounts on active markets, conduct controlled purchases, and build cases against high-volume vendors. The 2017 Hansa operation, where Dutch police operated the market for 27 days before announcing its closure, is the most notable example and collected buyer and vendor data that supported arrests across multiple countries.
3. Server Seizures
Physical server locations, even when obfuscated by Tor, can be identified through operational security mistakes by market operators. IP address leaks, domain registration errors, and misconfigured server software have all contributed to successful market takedowns.
4. Exit Scams Versus Takedowns
Not every market closure is a law enforcement success. Exit scams, where marketplace operators simply disappear with escrow funds, have become increasingly common. Abacus Market’s 2025 closure was assessed by most analysts as an exit scam rather than a law enforcement action.
The structural reality is that darknet markets are resilient by design. As Chainalysis noted, enforcement disruption produces displacement rather than permanent elimination. When Silk Road fell, AlphaBay launched. When AlphaBay fell, Hydra dominated. When Hydra fell, TorZon rose. The demand does not disappear. It migrates.
How Your Data Ends Up on a Darknet Marketplace
Most people whose data appears on darknet markets never made a mistake specific enough to explain how it happened.
The most common route is a data breach at a company you use. When a service is hacked, and its user database is stolen, that database, containing your email, hashed or plain-text password, and potentially your personal details and payment information, ends up for sale on a darknet market within hours or days. You did nothing wrong. The company holding your data failed to protect it.
The second most common route is infostealer malware. Infostealers are deployed through malvertising campaigns, drive-by downloads, and ClickFix attacks. Once on your device, they silently harvest every saved password, browser cookie, and autofill entry, packaging everything into a stealer log that is uploaded to the attacker’s server and then sold on the Russian Market or similar platforms.
Credential stuffing attacks take credentials from one breach and test them automatically against dozens of other services. If you reuse passwords across accounts, a breach at one service can expose all of them.
With a phishing attack, details of their credentials are given to the victims, who then enter them into fake-looking, plausible login screens. The credentials are then immediately passed onto the dark web marketplaces, where they will be sold.
Once your details are on a darknet marketplace, they could then be bought by any number of criminals to be used against you. Each set of details could then be resold again, and again to any number of other criminals, meaning attempts to compromise your accounts can last for months or years on the back of just one breach.
How to Protect Yourself

You cannot prevent your data from reaching a darknet marketplace if a company you use gets breached. But you can limit the damage and detect it quickly.
1. Monitor Whether Your Data Is Already There
The most important step is knowing when your data surfaces. Most people find out months after the fact, long after the damage is done.
DarkScout’s dark web monitoring continuously scans darknet markets, stealer log repositories, and breach databases for your email addresses, domains, and credentials. When something surfaces, you receive an immediate alert with context on what was found and what to do next.
Start with a free email scan to check whether your credentials are already exposed. For businesses, a website scan checks your domain’s exposure across known breach sources.
2. Use Unique Passwords for Every Account
Password reuse is the mechanism that turns one breach into dozens of compromised accounts. When your password from one service appears on a darknet market, credential stuffing tools test it automatically against every major service within hours.
Use a password manager to create and save a different, hard-to-crack password for every account or use a free password generator to create one instantly.
3. Enable Multi-Factor Authentication
If a password is lost and available on the dark net, MFA will prevent the majority of automated account takeovers. Enable it on every account that supports it, prioritizing email, banking, and any service connected to your work systems.
Be aware that push-based MFA is vulnerable to push bombing attacks. Where possible, use phishing-resistant MFA such as passkeys or hardware security keys for high-value accounts.
4. Act Immediately When You Get a Breach Notification
When a service notifies you of a breach, assume your credentials are already on a darknet market. Change the password for that service immediately. Change the same password on any other service where you used it. Check your other accounts for unusual activity. Run a dark web scan to see what data has been exposed.
5. Have a Response Plan Ready
For businesses, the time between credentials appearing on a darknet market and an attacker using them can be very short. Having a data breach response plan in place before an incident means your team knows exactly what to do the moment an alert arrives, rather than improvising under pressure.
Final Thoughts
Darknet marketplaces are not the mysterious, inaccessible underworld they are portrayed as in popular media. They are organized, functional platforms that have processed billions of dollars in transactions and have been directly responsible for some of the most damaging cyberattacks of the last decade.
Your data is one of their most consistently traded commodities. Stolen credentials, stealer logs, full identity packages, and corporate access listings cycle through these markets every day, bought and sold by criminals whose only job is to convert that data into money.
The best protection is not hoping your data never appears. It is knowing the moment it does, and having the systems in place to respond before the damage compounds.



